Creating a great Information Security Policy
26 Sep, 2017
What are the key points that should be included in an Information Security Policy?
Updated: January 2023
Including an Information Security Policy in your company documentation is an essential step to take if you want to build on your information security. As a necessity for the ISO 27001 Information Security standard, companies are required to have a detailed up to date policy in place, and it is best practice to ensure that you include the following:
Relevance
It goes without saying, any company policy should be relevant to the company. A small company would not be able to copy a policy from a global company, as it would not be relevant to how they operate. The best way to ensure your policy is relevant is by outlining how your company operates first, and meet these points when planning your policy.
Objective Setting Framework
A key part of ISO 27001 is setting objectives for the company to achieve in regards to their information security. Your policy should include the framework to follow when establishing these objectives, defining how the objectives are proposed, approved and reviewed.
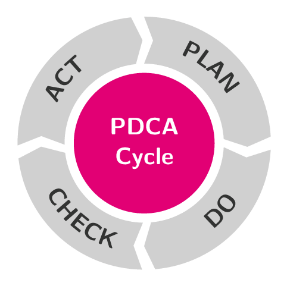 A common method used in the objective setting process is the PDCA cycle (Plan, Do, Check, Act). You would set your objectives in the Plan section, identify which stage you would class your objectives as achieved in the Do section, start measurement of your objectives in the Check section, and finally make improvements and amendments in the Act section.
A common method used in the objective setting process is the PDCA cycle (Plan, Do, Check, Act). You would set your objectives in the Plan section, identify which stage you would class your objectives as achieved in the Do section, start measurement of your objectives in the Check section, and finally make improvements and amendments in the Act section.
Commitment
Not only do your staff need to be committed to following your Information Security Policy, but also your management team need to state their commitment. This is usually done by including a statement in the policy expressing the commitment from management in regards to fulfilling the requirements of the policy and continually improving the Information Security Management System.
Scope
You can make reference to the scope of your Information Security Management System in your policy, so that it is clear what information your management system is protecting. This will cover all resources that hold information within your company and local network, just because a device may be out of the office does not mean it is out of the scope. As a part of ISO 27001, the auditor will check your scope to ensure that all elements of the management system are working within the scope, so you need to ensure that this includes all the relevant information.
Responsibilities
With an efficient management system also comes staff responsibilities, and these should be outlined in your policy so that everyone is clear on their roles. The staff member who is responsible for the day-to-day operations should be identified, as well as who is responsible on an executive level. This will be useful in the event of any incidents or when you need to conduct internal audits.
Measurement
The process for measuring your information security objectives can also be detailed in your policy. This would typically include who is responsible for measuring whether the objectives have been achieved, as well as who the results would be reported to and how often.
Regularly reviewed
To keep the policy relevant and up to date, it would have to be subject to regular reviews. There would typically be a designated member of staff who would review this and make amendments if necessary. If you don’t keep your policy up to date then it can soon fall behind and become irrelevant.
An ISO 27001 Information Security Management System is a systematic and pro-active approach to effectively managing risks to the security of your company’s confidential information. You can find out more about ISO 27001 by visiting our page here. Alternatively, you can speak to a member of our team on 0330 058 5551 or via email info@isoqsltd.com.
If you’re a client of ISO Quality Services, there is an Information Security Policy template available on the client area.
ISO Quality Services Ltd are proud to specialise in the implementation and certification of the Internationally recognised ISO and BS EN Management Standards.
Do you want to get ahead of your competition? Win more tenders or save time and money on reoccurring issues? Contact us today on 0330 058 5551 or email info@isoqsltd.com.
Alternatively, you can request a quote by filling out our enquiry form and a member of our team will be in touch shortly.